Cybersecurity: Protecting the digital frontier
Published: 01/25/2018
Updated: 03/16/2026
By Darryn Jones, Vice President of Emerging Technologies
In 1982, William Gibson, one of science fiction’s most visionary and distinctive voices, coined the term “cyberspace”. Two years later he published his seminal novel, Neuromancer, that described a virtual reality in which information is connected to a global computer network and experienced by humanity through hallucinatory experiences. Neuromancer’s protagonist, Henry Dorsett Case, battles “artificial intelligences” in this digital world to hack away information from global corporations for a fee.
Gibson’s description of “cyberspace” and its hacker anti-hero presaged today’s world of connected devices and the attendant security risks associated with the immense amount of data captured by these devices.
Cybersecurity Challenges by the Numbers
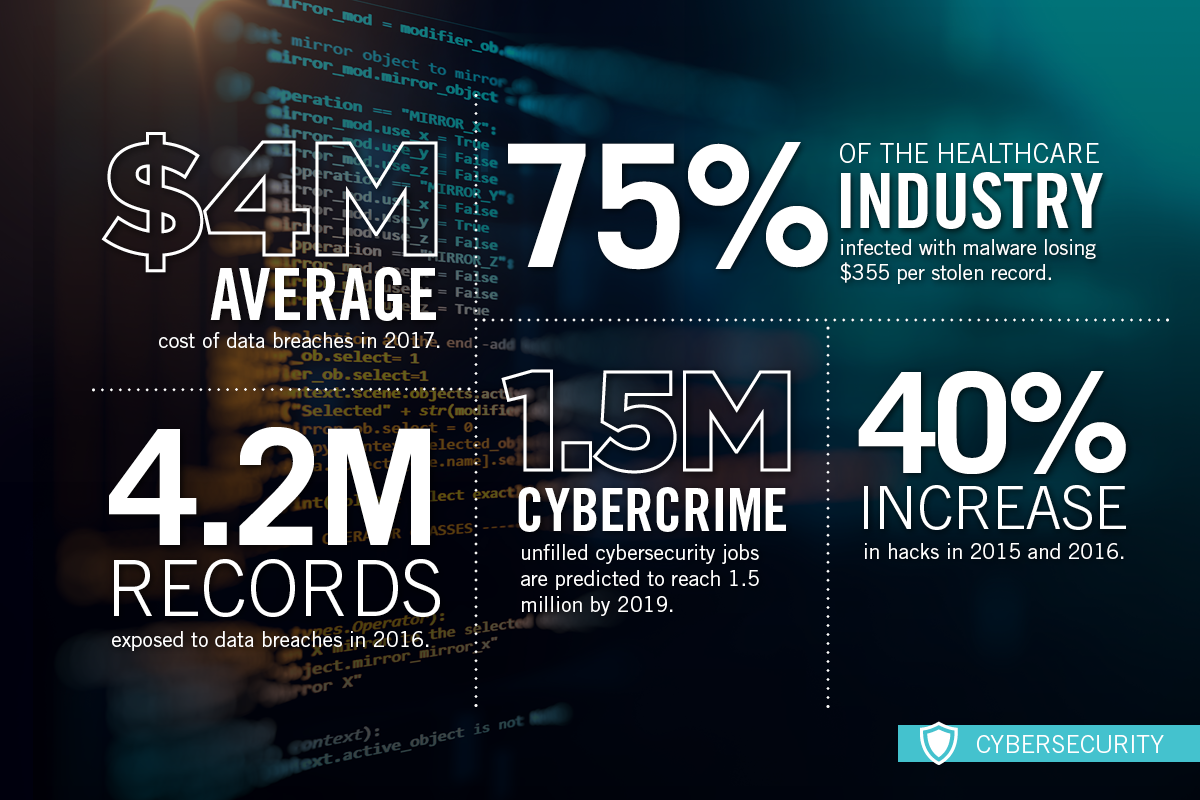
Cybersecurity infographic
Solving the Problem – What’s Next?
The internet of things (IoT) provides more attack vectors than ever before and companies are responding to these threats in new ways that will change the cybersecurity landscape of the future.
At the 3rd annual IoT Security Summit in New York City, startups and legacy companies in the cybersecurity space presented their solutions for protecting the digital frontier. The two central themes that emerged from the conference were SecDevOps and Hybrid Cloud Security and Blockchain.
SecDevOps
DevOps, an industry term of use for “development operations”, is a process by which development is informed by a deep understanding of how the system or technology operates. This process is designed to drive speed-to-market in both product deployment and updates, but security is often an afterthought. Enter SecDevOps, the process of integrating secure development best practices and methodologies into the development and deployments processes before it’s too late.
Businesses are embracing SecDevOps at a rapid clip and future innovation will be driven by improvements in both security-as-code (Sac) and infrastructure-as-code (IaC).
Hybrid Cloud Security and Blockchain
Expected cost savings, enhanced controls and improved regulatory compliance are driving an increase in cloud security adoption. However, there are still companies that need to keep some of their data on-premises for compliance with industry-specific regulation. Hybrid cloud solutions integrate public cloud infrastructure, such as Amazon Web Services (AWS) and Microsoft Azure, with a business’s on-premises resources. Hybrid solutions are expected to reduce the barriers to cloud adoption and allow access to innovation through public cloud investments.
One example of innovation leveraged through cloud infrastructure is the integration of blockchain protocols within the cloud technology stack. Providers such as Microsoft Azure are integrating blockchain platforms into their cloud services offerings in what has been coined Blockchain-as-a-Service (BaaS). With BaaS, companies can leverage existing cloud infrastructure to build business and security solutions powered by the blockchain. These solutions include multi-factor authentication across devices and the enhanced encryption of data.
The Greater Phoenix Region is an Emerging Cybersecurity Hub
Greater Phoenix, also known as The Connected Place, is one of the top markets in the nation to locate and expand cybersecurity operations due to its robust existing assets. Several cybersecurity 500-ranked companies call the region home, including Trusona, Continuum GRC, LifeLock, BeyondTrust and Mosaic 451. The Arizona Cyber Warfare Range (AZCWR) recently opened its second location in metro Phoenix, a 4,500-square-foot training center that will continue building a continuous stream of cybersecurity professionals to support companies growing and expanding in the region.
With our unique combination of talent, intellectual property and a robust cluster of cybersecurity firms, Greater Phoenix will remain a competitive location for companies developing innovative solutions to the privacy and security challenges that affect consumers and businesses alike. Learn more about our large cybersecurity presence here.
Greater Phoenix: The Connected Place
From wearables to autonomous vehicles, Greater Phoenix is “The Connected Place.”